

- 10 Posts
- 150 Comments


- TPLink Tapo line - I own those, requires internet / cloud access for setup, then can be viewed by any ONVIF capable software, VLC etc. You can cut their internet access and they mostly work, however timestamps and some features may break randomly;
- Reolink / AMCrest - no internet required, can be setup offline AND have a WebUI that allows full control over all functionality. Check the details of specific models, may vary a bit.
AMCrest is most likely be most offline friendly brand. Here’s a testimonial from another user:
I’ve been using Amcrest and foscam IP cameras at my home for the past several years. I have then connected to a no internet VLAN with an NVR. The models I’ve been using have an ethernet port and wifi. Setup was connecting to the ethernet port and then accessing the web ui in a browser to configure settings (most importantly turning on RTSP or ONVIF feeds)


I’ve been looking into some kind of simple SSO to handle this. I’m tired of entering passwords (even if it’s all done by the password manager) a single authentication point with a single user would be great.
Keycloak and friend are way too complex. Ideally I would like to have something in my nginx reverse proxies that would handle authentication at that level and tell the final app what user is logged on in some safe way.
it’s possible to have an email client download all the messages from Gmail and remove them from the server. I would like to set up a service on my servers to do that and then act as mail server for my clients. Gmail would still be the outgoing relay and the always-on remote mailbox, but emails would eventually be stored locally where I have plenty of space.
Do you really need this extra server? Why not just configure the account on Thunderbird and move the older / archival mail to a local folder? Or even drag and drop it out of Thunderbird to a folder and store the resulting files somewhere?
I’m just asking this because most people won’t need regular access to very old email and just storing the files on a NAS or something makes it easier.
I would go with Gitea or Forgejo (not sure how this is going to last) if you need a complete experience like a WebUI, issues, PR, roles and whatnot.
If you’re looking for just a git server then gitolite is very good and solid option. The cool thing about this one is that you create your repositories and add users using a repository inside the thing itself :).
Then you can use any Windows GUI you would like like Fork, SourceTree, your IDE etc…
Free Dyndns services seem to be a bit crap
Why do you say that? https://freedns.afraid.org/ and https://www.duckdns.org are very solid and if you’re looking for something more corporate even Cloudflare offers that service for free.
Yes, LetsEncrypt with DNS-01 challenge is the easiest way to go. Be it a single wildcard for all hosts or not.
Running a CA is cool however, just be aware of the risks involved with running your own CA.
You’re adding a root certificate to your systems that will effectively accept any certificate issued with your CA’s key. If your PK gets stolen somehow and you don’t notice it, someone might be issuing certificates that are valid for those machines. Also real CA’s also have ways to revoke certificates that are checked by browsers (OCSP and CRLs), they may employ other techniques such as cross signing and chains of trust. All those make it so a compromised certificate is revoked and not trusted by anyone after the fact.


If I connect it to my computer using a SATA to USB adapter instead of directly to the computer’s SATA, can it somehow affect the result of this scan?
It depends on how much power the disk requires and how much power the USB port can deliver. Also note that USB-A is the worst connector out there when it comes to mechanical reliability - it only takes a finger on the plug to screw whatever data transfer is going on.
For external disks (both 2.5 and 3.5") I’ve a bunch of this powered USB disk enclosures. They’ve a good chip, are made of metal and a USB-B 3 port. You can connect those to any USB-A device and you’ll know that only one side might fail… if you’ve USB-C a cable like this tends to be more reliable.
Another good option, if you’ve USB-C and you want something more portable is to get a USB-C disk enclosure as those will be able to deliver more power and be more reliable.
PS: avoid whatever garbage Orico is selling, Inateck is much better.
How do I know all of this? Well I happen to work with WordPress professionally as the lead developer for an agency where I manage literally hundreds of WordPress sites and host all of them myself on servers I manage for them (not shared hosting reselling).
I used to have the same role and before that I managed a shared hosting provider. At that job the majority of websites hosted there were WordPress and customers would pay us to develop or fix stuff sometimes.
The vast majority of those “extensions” (plugins) are horribly made and are security nightmares,
Yes, this is true and a problem, but at the same time the WordPress ecosystem, as you know, gets shit done.
I also had some experiences with PrestaShop/Magento and they are even worse than WordPress. You still have the performance issues, the 3rd party poorly developed themes and plugins and a convoluted API.
WooCommerce powers 38% of the online stores out there…
WordPress’s data structure is not properly suited for an e-commerce site
To be fair WordPress’ data structure is not properly suited for anything, not even posts and pages, let alone block structures and whatever but the truth is that it works and delivers results. Same goes for WooCommerce, if you don’t want to be hostage of Shopify and your objective actually selling shit instead of spending all your time developing store software then WooCommerce is the way to go.
WooCommerce also has an extensive extension list, integrations with all the payment providers out there and it’s easy to get help / support be it free or paid.
and it’s a resource hog.
Did you ever they Magento or PrestaShop? Doesn’t seem like you did as those are store-first solutions and they’re all slower and more of a resource hog than WP can ever be.


https://github.com/philpagel/debian-headless
It is possible but I wouldn’t do it. Too much effort for too little result.
Just plug your main monitor / keyboard into the server, run the setup and don’t install a DE. Afterwards login, enable SSH, unplug the monitor and do whatever you need over SSH.
Let’s face it, you’ll have to do this procedure once every xyz years, there’s no point in complicating this stuff. Also depending on your motherboard you may or may not be able to boot into the installer without a screen / keyboard attached. Another option is to install the OS in another computer and the move the hard drive to the target server - this is all fine until you run into UEFI security or another detail and it doesn’t boot your OS.
Step 1: get a cheap VPS, or even a free one (https://www.oracle.com/cloud/free/)
Step 2: If you’ve a static IP at home great, if you don’t get a dynamic DNS from https://freedns.afraid.org/ or https://www.duckdns.org/
Step 3: Install nginx on the VPS and configure it as reverse proxy to your home address. Something like this:
server {
listen 80;
server_name example.org; # your real domain name you want people to use to access your website
location / {
proxy_pass http://home-dynamic-dns.freeprovider... # replace with your home server IP or Dynamic DNS.
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_redirect off;
}
}
Step 4: Point your A record of example.org to your VPS.
Step 5: there’s a potential security issue with this option: https://nginx.org/en/docs/http/ngx_http_realip_module.html#set_real_ip_from and to get around this you can do the following on the home server nginx config:
http {
(...)
real_ip_header X-Real-IP;
set_real_ip_from x.x.x.x; # Replace with the VPS IP address.
}
This will make sure only the VPS is allowed to override the real IP of the client.
Step 6: Once your setup works you may increase your security by using SSL / disabling plain HTTP setup letsencrypt in both servers to get valid SSL certificates for real domain and the dynamic DNS one.
Proceed to disable plain text / HTTP traffic. To do this simply remove the entire server { listen 80 section on both servers. You should replace them with server { listen 443 ssl; so it listens only for HTTPs traffic.
Step 7: set your home router to allow incoming traffic in port 443 and forward it into the home server;
Step 8: set the home server’s firewall to only accept traffic coming from outside the LAN subnet on port 443 and if it comes from the VPS IP. Drop everything else.
Another alternative to this it to setup a Wireguard tunnel between your home server and the VPS and have the reverse proxy send the traffic through that tunnel (change proxy_pass to the IP of the home server inside the tunnel like proxy_pass http://10.0.0.2). This has two advantages: 1) you don’t need to setup SSL at your home server as all the traffic will flow encrypted over the tunnel and 2) will not require to open a local port for incoming traffic on the home network… however it also has two drawbacks: you’ll need a better VPS because WG requires extra processing power and 2) your home server will have to keep the tunnel connected and working however it will fail. Frankly I wouldn’t bother to setup the tunnel as your home server will only accept traffic from the VPS IP so you won’t gain much there in terms of security.


Total e-waste and a power draw (almost constant 95W). Even a Raspberry Pi 4 Model B can beat it to oblivion:
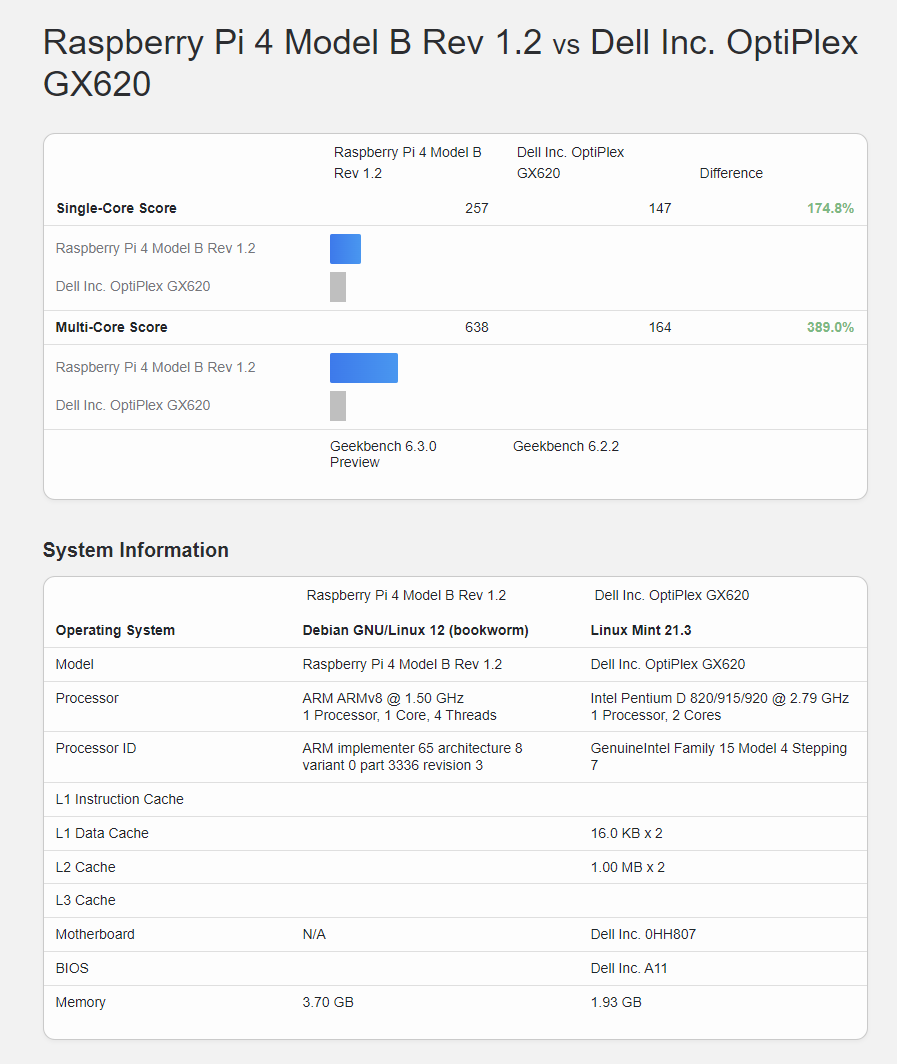
https://browser.geekbench.com/v6/cpu/compare/6390478?baseline=5583060
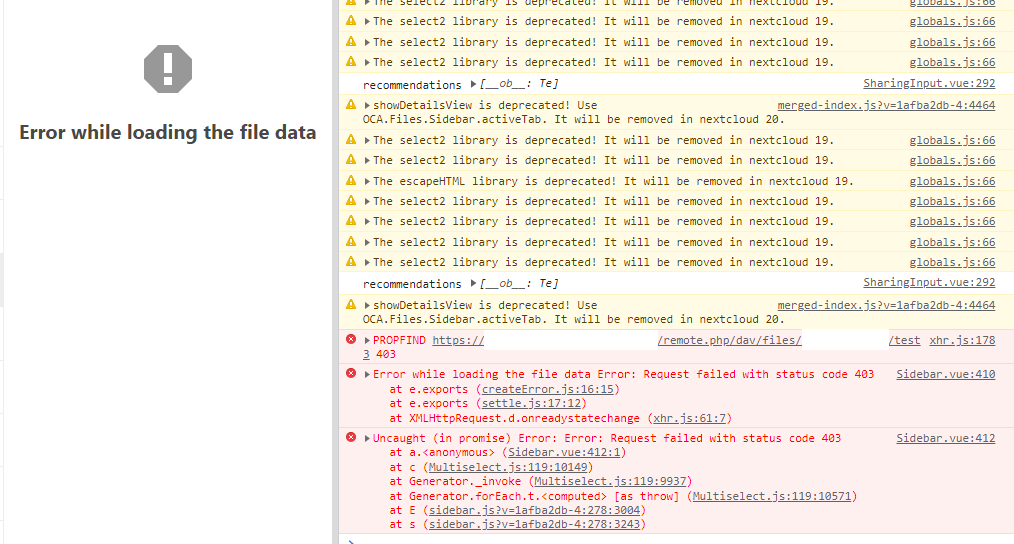
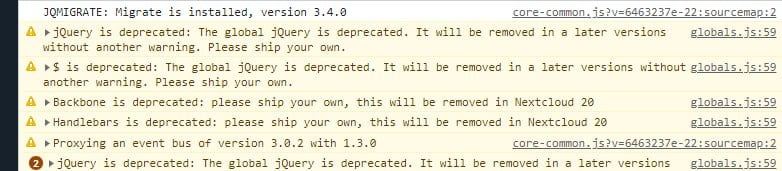
The point is that every single feature they try to add to it ends up as yet another buggy thing that never gets fixed. They should focus on making the core things works decently instead of adding new features. After all this time they didn’t get the sync to be as reliable as Syncthing, why would they venture into webmail’s and whatnot ?
Well, how much wifi and open-source do you really want?
If you are willing to go with commercial hardware + OpenWRT you might want to check the table of hardware at https://openwrt.org/toh/views/toh_available_16128_ax-wifi and https://openwrt.org/toh/views/toh_available_864_ac-wifi. Solid picks for the future might be the Netgear WAX2* line (no USB), the GL.iNet GL-MT6000, ASUS RT-AX59U, Belkin RT1800, Belkin RT3200, Linksys E7350, Linksys E8450. If you don’t mind having older wifi a Netgear R7800 is solid.
For a full open-source hardware and software experience you need a more exotic brand like this https://www.banana-pi.org/en/bananapi-router/. The BananaPi BPi R3 and here is a very good option with a 4 core CPU, 2GB of RAM Wifi6 and two 2.5G SFP ports besides the 4 ethernet ports. There’s also an upcoming board the BPI-R4 with optional Wifi 7 and 10G SPF.
Side note: while there are things like OPNsense and pfSense that may make sense in some cases you most likely don’t require that. You’ve a small network and OpenWRT will provide you with a much cleaner open-source experience and also allow for all the customization you would like. Another great advantage of OpenWRT is that with a great router like the BananaPi BPi R3 you’ve the ability to install 3rd party stuff in your router, you may even use qemu to virtualize stuff like your Pi-Hole on it or simply run docker containers.


They’re a finite resource and should be limited to a fixed number per human being. And only transferred for free not resold.
While I don’t agree with the free transfer I agree with the the other part. ICANN should fine and obliterate registrars that keep domains for themselves and individual hoarders.

 English
English- •
- domainnamewire.com
- •
- 6M
- •
There seems to be a request to add this to the new Thunderbird CaldDAV features: https://connect.mozilla.org/t5/ideas/support-vjournal-in-thunderbird/idi-p/46295
How much wifi and open-source do you really want?
If you are willing to go with commercial hardware + open source firmware (OpenWrt) you might want to check the table of hardware of OpenWrt at https://openwrt.org/toh/views/toh_available_16128_ax-wifi and https://openwrt.org/toh/views/toh_available_864_ac-wifi. One solid pick for the future might be the Netgear WAX2* line or the GL.iNet GL-MT6000. One of those models is now fully supported the others are on the way. If you don’t mind having older wifi a Netgear R7800 is solid.
For a full open-source hardware and software experience you need a more exotic brand like this https://www.banana-pi.org/en/bananapi-router/. The BananaPi BPi R3 and here is a very good option with a 4 core CPU, 2GB of RAM Wifi6 and two 2.5G SFP ports besides the 4 ethernet ports. There’s also an upcoming board the BPI-R4 with optional Wifi 7 and 10G SPF.
Both solutions will lead to OpenWRT when it comes to software, it is better than any commercial firmware but be aware that it only support wifi hardware with open-source drives such as MediaTek. While MediaTek is good and performs very well we can’t forget that the best performing wifi chips are Broadcom and they use hacks that go behind the published wifi standards and get it go a few megabytes/second faster and/or improve the range a bit.
DD-WRT is another “open-source” firmware that has a specific agreement with Broadcom to allow them to use their proprietary drivers and distribute them as blob with their firmware. While it works don’t expect compatibility with newer hardware nor a bug free solution like OpenWRT is.
There are also alternatives like OPNsense and pfSense that may make sense in some cases you most likely don’t require that. You’ve a small network and OpenWRT will provide you with a much cleaner open-source experience and also allow for all the customization you would like. Another great advantage of OpenWRT is that you’ve the ability to install 3rd party stuff in your router, you may even use qemu to virtualize stuff like your Pi-Hole on it or simply run docker containers.
It depends on your needs. How much do you value your data? Can you re-create / re-download it in case of a disk failure?
In some case, like a typical home users with a few writes per day or even week simply having a second disk that is updated every day with rsync may be a better choice. Consider that if you’re two mechanical disks spinning 24h7 they’ll most likely fail at the same time (or during a RAID rebuild) and you’ll end up loosing all your data. Simply having one active disk (shared on the network and spinning) and the other spun down and only turned on once a day with a cron rsync job mean your second disk will last a LOT longer and you’ll be safer.
If you run your stuff in containers then Proxmox (I aways install it on top of Debian) is your hypervisor is your base system
I believe you’re missing my point. Cockpit also works as an hypervisor for most people, a very light and stable one, besides…
If you’re running containers on Proxmox then you’re running LXC containers… why not just use LXD/Incus (also another hypervisor) to manage those containers that is considerably lighter, comes by default in the Debian repository, was designed to manage LXC container (not hacked around like Proxmox was) and isn’t mostly made by a for profit entity that sometimes likes to hold important patches on their subscription-only repositories? Or constantly nag you to buy a subscription?
Dude the guy is running on system with restricted resources and you’re suggesting the most bloated and prone to fail thing ever.
The OP would be way better with Debian + Cockpit (also provider a webUI and virtual machine manager) or Debian + LXD/LXC (containers + VMs, optional webUI). Both of those solutions are way lighter and won’t mess your base system.
My Debian Hypervisor do have a DE (GNOME) to be able to easily access virtual machines with virt-manager
Well I guess that depends on your level of proficiency with the cli. I personally don’t want a DE running ever, in fact my system doesn’t even have a GPU nor a CPU that can do graphics.
With that said, do you know about Cockpit? It provides you with a very light WebUI for any server and has a virtual machine manager as well.
I don’t mind helping my friends install their openvpn client and certificate and it’s nice to not have my services bombarded with failed connection attempts.
Yes I know the feeling ahahah. Now you should consider Wireguard, it’s way easier and lighter. Check out the links I provided, there’s a nice WebUI to provision clients there.
Totally agree. :) Here’s a quick and nice guide: https://www.digitalocean.com/community/tutorials/how-to-secure-nginx-with-let-s-encrypt-on-debian-11

 English
English- •
- 8M
- •

 English
English- •
- github.com
- •
- 8M
- •

 English
English- •
- www.cnx-software.com
- •
- 10M
- •

 English
English- •
- tadeubento.com
- •
- 1Y
- •

 English
English- •
- tadeubento.com
- •
- 1Y
- •

 English
English- •
- joshmadison.com
- •
- 1Y
- •

 English
English- •
- 1Y
- •








… NO internet required, no apps, nothing. Just a WebUI on a browser.